If you’ve been searching for a clear, practical guide to tls protocol explained, you’re likely trying to understand how secure communication actually works behind the scenes of the web. Whether you’re a developer, IT professional, or simply security‑conscious, you need more than surface‑level definitions—you need a breakdown that connects encryption theory to real‑world application.
This article is designed to do exactly that. We’ll walk through how the TLS protocol establishes secure connections, how certificates and handshakes function, and why modern encryption standards matter for protecting sensitive data. We’ll also clarify common misconceptions and highlight how TLS fits into broader cybersecurity and system optimization practices.
Our insights are grounded in deep research across cryptography standards, network security frameworks, and real‑world implementation models used in modern computing environments. By the end, you’ll have a practical, technically accurate understanding of TLS—and the confidence to apply that knowledge effectively.
Securing Your Digital Conversations: A Deep Dive into TLS
Every time you log in, shop, or stream, data travels across hostile networks. The tls protocol explained here shows how that data stays private.
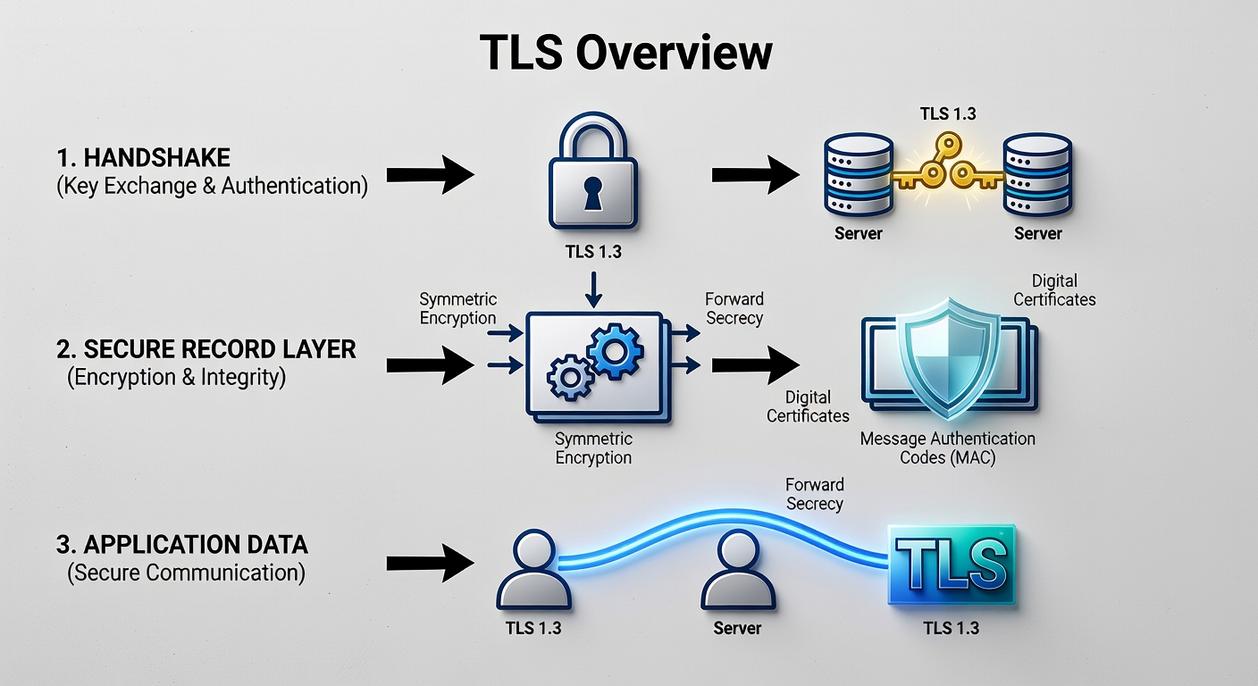
Step 1: The Handshake. Your browser and server agree on:
- Encryption algorithms
- Session keys
- Digital certificates
A digital certificate is a verified public key that proves a server’s identity (think passport control for websites).
Step 2: Key Exchange. Using asymmetric encryption, they create a shared secret.
Step 3: Secure Communication. Symmetric encryption protects speed and integrity.
Competitors rarely clarify TLS ensures message authentication, blocking tampering in transit.
What is TLS? The Unseen Guardian of Your Internet Activity
Transport Layer Security (TLS) is the standard technology that keeps internet connections secure, protecting sensitive data as it travels between two systems. In plain terms, the tls protocol explained simply is the lock on the digital door between your browser and a website.
At its core, TLS supports the “CIA” triad: Confidentiality (encryption, meaning outsiders can’t read your data), Integrity (the data hasn’t been altered in transit), and Authentication (verifying identities). Without these three pillars, online banking would feel like sending cash through the mail.
Now compare SSL vs. TLS. SSL (Secure Sockets Layer) was the original security protocol; TLS is its modern, stronger successor. Think VHS vs. streaming—same goal, vastly better execution.
In other words, TLS works like a tamper-proof, sealed envelope delivered by a trusted courier. Only the intended recipient can open it, and if it’s been tampered with, you’ll know immediately.
The Digital Handshake: How TLS Establishes a Secure Connection
When you type a URL into Chrome or Firefox and see that small padlock icon, you’re witnessing a quiet negotiation happening behind the scenes. Think of it as a digital handshake between your browser (the client) and a website’s server. Before any sensitive data—passwords, credit card numbers, API tokens—travels across the wire, both sides agree on the rules of engagement.
In other words, this is the tls protocol explained in practical terms.
Step 1 – The “Client Hello”
First, the client initiates contact with a Client Hello message. It includes:
- The TLS version it supports
- A list of cipher suites (encryption algorithm combinations)
- A unique random number (called the client random)
A cipher suite defines how key exchange, encryption, and message authentication will work together. In enterprise environments—say, fintech platforms in New York or health-tech systems bound by HIPAA—this list is carefully curated to exclude weak algorithms (because compliance teams do check).
Step 2 – The “Server Hello” & Certificate
Next, the server replies with a Server Hello. It selects one cipher suite from the client’s list and sends:
- Its own random number
- Its SSL/TLS certificate
The certificate proves the server’s identity. It’s issued by a trusted Certificate Authority (CA), such as DigiCert or Let’s Encrypt. According to Google’s Transparency Report, over 95% of web traffic in Chrome is now encrypted with HTTPS, which relies on this certificate-based trust model.
Step 3 – Verification and Key Creation
Now comes the critical moment. The client verifies the certificate against its trusted CA store. If valid, both sides use the two random numbers and the chosen algorithm to independently generate identical session keys—temporary symmetric keys used for fast encryption.
(They never actually send the session key itself—like agreeing on a secret recipe without emailing it.)
Step 4 – The “Finished” Message
Finally, both client and server send encrypted Finished messages. If each side can decrypt and validate them, the handshake is complete.
From that point forward, all communication is encrypted with the new session keys—whether you’re logging into a SaaS dashboard or configuring tunnels described in a practical guide to vpn protocols and how they work.
The padlock appears. The channel is secure. And the conversation can begin.
The Three Pillars of TLS Protection Explained
Transport Layer Security rests on three core ideas: confidentiality, authentication, and integrity. Together, they form the backbone of what many call the tls protocol explained in simple terms.
Pillar 1 – Encryption (Confidentiality)
After the TLS handshake, the client and server generate shared session keys, which are temporary symmetric encryption keys. Symmetric encryption means the same key locks and unlocks the data. Every byte transmitted is mathematically scrambled, making intercepted traffic unreadable to outsiders.
According to IBM’s 2023 Cost of a Data Breach Report, the global average data breach cost reached $4.45 million. Strong encryption significantly reduces exposure when traffic is intercepted. Even if a hacker captures packets on public Wi‑Fi (yes, even at your favorite coffee shop), without the session key, the data appears as meaningless ciphertext. Pro tip: Always look for HTTPS in the browser bar when transmitting sensitive data.
Pillar 2 – Authentication (Identity)
Authentication relies on the SSL/TLS certificate, which acts like a digital passport. Issued by a trusted Certificate Authority (CA), it cryptographically verifies that the server truly owns the domain.
Google’s Transparency Report shows that over 95% of Chrome traffic is now encrypted via HTTPS, largely due to widespread certificate adoption. This validation blocks man-in-the-middle attacks, where an attacker pretends to be a legitimate server (think Mission: Impossible, but less glamorous and more code).
Pillar 3 – Integrity (Reliability)
Integrity is enforced through a Message Authentication Code (MAC). A MAC is a cryptographic checksum attached to each data block. When received, the system recalculates and compares it. If even one bit changes, verification fails.
This ensures information arrives exactly as sent—no silent tampering, no hidden alterations, just verified trust.
Open your browser and look at the address bar. If you see “https://” and a padlock icon, you’re using Transport Layer Security (TLS)—the encryption standard that protects data in transit. In fact, Google reports that over 95% of Chrome traffic now loads over HTTPS, showing how widespread TLS has become.
However, TLS isn’t limited to websites. Email servers use it with SMTP, VoIP apps encrypt calls, and mobile apps secure API requests. This is tls protocol explained in real life.
Moreover, TLS 1.3 reduces handshake steps, cutting latency by one round trip (Cloudflare), making secure connections noticeably faster on devices.
Your data’s first and strongest line of defense is TLS. By now, you know it isn’t just another browser feature; it’s the protocol that makes secure online interactions possible. In simple terms, it creates a private channel over a public internet through authentication (verifying identity), encryption (scrambling data), and integrity checks (detecting tampering). Without it, your information would travel like a postcard; with it, it’s sealed like a vault. Look for https and the padlock icon before entering passwords or payment details. If you’re unsure think of tls protocol explained as your bodyguard—quiet, constant, and essential, like Jarvis for browser.
You came here looking for clarity on tls protocol explained, and now you have a practical understanding of how it encrypts data, authenticates connections, and protects information in transit. Instead of vague technical jargon, you’ve seen how TLS actually works behind the scenes—and why it’s critical for secure browsing, secure apps, and modern digital communication.
The reality is simple: without strong encryption protocols in place, your data is exposed to interception, manipulation, and costly breaches. Whether you’re managing a website, building an app, or optimizing enterprise systems, overlooking transport security isn’t just a technical gap—it’s a risk to trust, performance, and compliance.
Secure Your Systems with Confidence
Now that you understand tls protocol explained, the next step is implementation and optimization. Don’t leave your systems vulnerable or misconfigured. Take action to audit your current security setup, update outdated certificates, and ensure modern TLS configurations are properly deployed.
If you want expert-backed insights on encryption, AI-driven security optimization, and cutting-edge computing practices, start applying proven strategies today. The right security foundation prevents breaches before they happen—so review your infrastructure now and strengthen your protection immediately.


 Founder & Chief Visionary Officer (CVO)
Selviana Vaelvessa writes the kind of device optimization techniques content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Selviana has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Device Optimization Techniques, AI and Machine Learning Ideas, Data Encryption and Network Protocols, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Selviana doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Selviana's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to device optimization techniques long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.
Founder & Chief Visionary Officer (CVO)
Selviana Vaelvessa writes the kind of device optimization techniques content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Selviana has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Device Optimization Techniques, AI and Machine Learning Ideas, Data Encryption and Network Protocols, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Selviana doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Selviana's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to device optimization techniques long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.
